2013 Все новости SSL технологий
С 7 ноября 2012 года стартовала акция WebTrust Ukraine по поставке ссл сертификатов Symantec group ( VeriSign, Thawte, GeoTrust ) для учебных заведений Украины со скидкой до 75%
ВебТраст Украина сообщает о ряде важных изменений в политике и стандартах выпуска SSL сертификатов с 1 июля 2012 года. Эти изменения связаны с новыми требованиями политики CABForum.
Мы приветствуем CA / Browser Forum и высоко оцениваем ее вклад в ее будущее развитие безопасности. Унификация требований имеет важное значение для обеспечения безопасности и надежности сети Интернет. Это безопасность и доверие обеспечения должна исходить от общественности и прозрачный процесс с открытым участием пострадавших, Интернет развивается на открытом, прозрачном и многостороннем управлении и стандартизации процессов, и координации действий между этими процессами и участниками рынка, о чем свидетельствуют такие организации, как IETF, ICANN, and W3C.
О ВебТраст Украина
Центр сертификации сайтов и верификации компаний WebTrust® Украина создан для решения проблемы установления легальности сайтов, представляющих коммерческие организации и физические лица, путем их сертификации.
Основное предназначение WebTrust® Украина – повысить доверие к сайту, тем самым, поднять его статус, посещаемость, коэффициент возврата постоянных посетителей, объем продаж товаров и услуг и иные показатели, связанные с преодолением порога недоверия и неуверенности.
Веб Траст Украина производит верификацию компаний и выдает информацию на трех языках: украинском, русском и английском языках.
Верификация компаний и выдача сертификатов производится с учетом норм законодательства Украины и учетом сложившихся национальных традиций.
* Веб Траст Украина верифицирует информацию о компании и о доменах, но не контролирует содержание ресурса. WebTrust® Ukraine не производит мониторинг содержимого сайта.
Symantec Strengthens SSL Security and Trust with Updated CA/B Forum Requirements
VeriSign Authentication Services, now part of Symantec, is adopting the latest Certificate Authority /Browser (CA/B) Forum Baseline Requirements1 designed to further strengthen the security and trust that comes with SSL Certificates. Here is a summary of the CA/B guidelines and Symantec’s plans and schedule:
- Maximum validity period of certificates:
- Certificates issued after July 1st, 2012 MUST have a validity period no greater than 60 months.
- Except for certain conditions, certificates issued after April 1st, 2015 MUST have a validity period no greater than 39 months.
⁃ Symantec’s adoption:- all new SSL certificates issued AFTER the June 7th, 2012 release will have a maximum validity period of up to 4 years.
- EV SSL certificates will continue to have a maximum validity period of up to 2 years.
- Subject Alternative Name (SAN) extension and Subject Common Name (CN) field
- The SAN extension MUST contain at least one entry. Each entry MUST contain the Fully Qualified Domain Name (FQDN) or the IP address of a server. The CA MUST confirm that the Applicant controls the FQDN or IP address or has been granted the right to use it by the Domain Name Registrant or IP address assignee, as appropriate.
- Wildcard FQDNs are permitted.
- Certificate Authorities SHALL notify applicants starting on July 1st, 2012, that the issuance of a certificate with a SAN or CN field containing a Reserved IP Address or Internal Server Name, is being phased out. The practice will no longer be valid in October 2016.
- Also as of July 1st, 2012, the Certificate Authority SHALL NOT issue a certificate with an expiration date later than 1st of November, 2015 with a SAN extension or CN field containing a Reserved IP Address or Internal Server Name.
- Effective 1st October 2016, Certificate Authorities SHALL revoke all unexpired certificates whose SAN extension or CN field contains a Reserved IP Address or Internal Server Name.
- The use of CN field is discouraged, but not prohibited. If present, this field MUST contain a single IP address or FQDN that is one of the values contained in the Certificate’s SAN extension.
⁃ Symantec’s adoption:- CN is included in SAN fields at no additional charge. This update does not impact the certificate workflow and there is no partner action required.
- Starting with our release in April 2012, Symantec will not issue a certificate with an expiration date later than November 1st, 2015 that has a SAN or CN field containing a Reserved IP Address or Internal Server Name. In addition, Symantec will revoke any unexpired certificate that has a SAN or CN with a reserved IP or non-FQDN, effective October 1st 2016.
- Symantec will mandate the inclusion of the following in OV and EV SSL certificates:
- Locality Name
- State or Province Name (where applicable)
- Country Name
- The following two parameters are OPTIONAL:
- Street Address
- Postal Code
The Organization and Country fields are being removed from Domain validated certificates. This does not impact the certificate workflow and there is no partner action required. Symantec will be phasing this change in by brand over the coming weeks and have it completed by July 1st.
Note: Starting January 1st, 2014, the industry is discontinuing the use of 1024-bit key length on SSL certificates and Code Signing products. This is in compliance with NIST Special Publication 800-131A. Beginning January 2012, 2048-bit keys will be enforced on all new multi-year Code Signing products and SSL certificates. All Code Signing products and SSL certificates will be required to have 2048-bit key lengths after December 31st, 2013. Please plan the adoption of 2048-bit key lengths in your Code Signing products and SSL certificates accordingly.
Any forward-looking indication of plans for products is preliminary and all future release dates are tentative and are subject to change. Any future release of the product or planned modifications to product capability, functionality, or feature are subject to ongoing evaluation by Symantec, and may or may not be implemented and should not be considered firm commitments by Symantec and should not be relied upon in making purchasing decisions.
- 06/19 http://www.symantec.com/about/news/release/article.jsp?prid=20120619_01 Symantec Survey Reveals Online File Sharing Poses Great Security Risks to SMBs">Symantec Survey Reveals Online File Sharing Poses Security Risks to SMBs
- 06/14 http://www.symantec.com/about/news/release/article.jsp?prid=20120614_01 Sean Forkan Appointed New Country Manager for Symantec Canada">Sean Forkan Appointed New Country Manager for Symantec Canada
- 06/13 http://www.symantec.com/about/news/release/article.jsp?prid=20120613_01 Symantec Finds Accidental Entrepreneurs Leverage Scalable Technology to Fast-Track Growth">Symantec Finds Accidental Entrepreneurs Leverage Scalable Technology
- 06/11 http://www.symantec.com/about/news/release/article.jsp?prid=20120611_02 Symantec Prices $1.0 Billion Senior Unsecured Note Offering">Symantec Prices $1.0 Billion Senior Unsecured Note Offering
- 06/11 http://www.symantec.com/about/news/release/article.jsp?prid=20120611_01 Symantec to Deliver Disaster Recovery as a Service on Windows Azure">Symantec to Deliver Disaster Recovery as a Service on Windows Azure
- 06/05 http://www.symantec.com/about/news/release/article.jsp?prid=20120605_01 Symantec Bolsters Commitment to SMB Customers and Partners">Symantec Bolsters Commitment to SMB Customers and Partners
- 05/30 http://www.symantec.com/about/news/release/article.jsp?prid=20120530_02 Symantec Positioned as a Leader in Magic Quadrant for E-Discovery Software">Symantec Positioned as a Leader in Magic Quadrant for E-Discovery Software
- 05/30 http://www.symantec.com/about/news/release/article.jsp?prid=20120530_01 Symantec Launches SymEd for K-12 and Higher Education">Symantec Launches SymEd for K-12 and Higher Education
- 05/25 http://www.symantec.com/about/news/release/article.jsp?prid=20120525_01 Symantec Announces Tender Offer for VeriSign Japan KK">Symantec Announces Tender Offer for VeriSign Japan KK
- 05/15 http://www.symantec.com/about/news/release/article.jsp?prid=20120515_01 Symantec to Webcast 2012 Financial Analyst Day">Symantec to Webcast 2012 Financial Analyst Day
- 05/14 http://www.symantec.com/about/news/release/article.jsp?prid=20120514_01 SMBs Are Adopting Virtualization, Cloud and Mobility for Improved Disaster Preparedness">SMBs Adopting Virtualization, Cloud and Mobility for Disaster Preparedness
- 05/09 http://www.symantec.com/about/news/release/article.jsp?prid=20120509_01 Symantec Solutions Achieve Common Criteria Certifications">Symantec Solutions Achieve Common Criteria Certifications
- 05/08 http://www.symantec.com/about/news/release/article.jsp?prid=20120508_02 Symantec Modernizes Data Protection with Integrated Backup and Deduplication Appliances">Symantec Protects Data with Integrated Backup and Deduplication Appliances
- 05/08 http://www.symantec.com/about/news/release/article.jsp?prid=20120508_01 Symantec Fosters Secure Mobile Productivity with Enterprise Mobility Enhancements">Symantec Fosters Secure Productivity with Enterprise Mobility Enhancements
- 05/03 http://www.symantec.com/about/news/release/article.jsp?prid=20120503_04 Norton 2013 Public Betas Now Available">Norton 2013 Public Betas Now Available
- 05/03 http://www.symantec.com/about/news/release/article.jsp?prid=20120503_03 Norton 360 Everywhere Now Available For Multi-Platform, Multi-Device Protection">Norton 360 Everywhere Now Available
- 05/03 http://www.symantec.com/about/news/release/article.jsp?prid=20120503_02 Symantec to Speak at Upcoming Investor Conferences">Symantec to Speak at Upcoming Investor Conferences
- 05/03 http://www.symantec.com/about/news/release/article.jsp?prid=20120503_01 Symantec Expands Security Capabilities for Managed Service Providers with the Availability of the Symantec Endpoint Protection Management Plug-in 1.5 for Kaseya">Symantec Provides MSPs with Symantec Endpoint Protection Plugin for Kaseya
- 05/02 http://www.symantec.com/about/news/release/article.jsp?prid=20120502_01 Symantec Reports Fourth Quarter and Fiscal Year 2012 Results">Symantec Reports Fourth Quarter and Fiscal Year 2012 Results
- 04/29 http://www.symantec.com/about/news/release/article.jsp?prid=20120429_01 Annual Symantec Internet Security Threat Report Reveals 81 Percent Increase in Malicious Attacks">Internet Security Threat Report Reveals 81% Increase in Malicious Attacks
- 04/25 http://www.symantec.com/about/news/release/article.jsp?prid=20120425_02 Norton and Facebook Partner to Make the Web Safer">Norton and Facebook Partner to Make the Web Safer
- 04/25 http://www.symantec.com/about/news/release/article.jsp?prid=20120425_01 Symantec Named 2012 CRN Channel Champion for Client Security and Backup/Recovery Software">Symantec Named 2012 CRN Channel Champion
- 04/24 http://www.symantec.com/about/news/release/article.jsp?prid=20120424_02 Symantec Reports Preliminary Fiscal Fourth Quarter 2012 Results">Symantec Reports Preliminary Fiscal Fourth Quarter 2012 Results
- 04/24 http://www.symantec.com/about/news/release/article.jsp?prid=20120424_01 Norton Solves Password Pain with Identity Safe">Norton Solves Password Pain with Identity Safe
- 04/23 http://www.symantec.com/about/news/release/article.jsp?prid=20120423_01 New Norton Secured Seal is the Most Recognized Trust Mark on the Internet">New Norton Secured Seal Is the Most Recognized Trust Mark on the Internet
- 04/19 http://www.symantec.com/about/news/release/article.jsp?prid=20120419_01 Symantec Achieves Highest Number of SSL Certificates Issued Globally">Symantec Achieves Highest Number of SSL Certificates Issued Globally
- 04/16 http://www.symantec.com/about/news/release/article.jsp?prid=20120416_01 Symantec Completes Acquisition of Nukona">Symantec Completes Acquisition of Nukona
- 04/11 http://www.symantec.com/about/news/release/article.jsp?prid=20120411_01 Symantec Named Best Places to Work on HRC 2012 Corporate Equality Index">Symantec Named Best Places to Work on HRC 2012 Corporate Equality Index
- 04/04 http://www.symantec.com/about/news/release/article.jsp?prid=20120404_01 Norton Launches Industry’s First Security Membership Offering">Norton Launches Industry’s First Security Membership Offering
- 04/02 http://www.symantec.com/about/news/release/article.jsp?prid=20120402_02 Northeastern Illinois University Leverages Symantec Solutions to Boost Efficiency, Improve Backup and Tighten Security in Virtual and Physical IT Environments">Northeastern Illinois University Uses Symantec Backup & Security Solutions
- 04/02 http://www.symantec.com/about/news/release/article.jsp?prid=20120402_01 Symantec to Webcast Quarterly Earnings Call">Symantec to Webcast Quarterly Earnings Call
- 03/30 http://www.symantec.com/about/news/release/article.jsp?prid=20120330_01 Symantec Completes Sale of Huawei Symantec Joint Venture to Huawei">Symantec Completes Sale of Huawei Symantec Joint Venture to Huawei
- 03/27 http://www.symantec.com/about/news/release/article.jsp?prid=20120327_01 Premiere Global Sports Deploys Symantec Solutions to Secure and Back Up Virtual Systems">Premiere Global Sports Uses Symantec to Secure and Back Up Virtual Systems
- 03/26 http://www.symantec.com/about/news/release/article.jsp?prid=20120326_01 Nikon Corporation Takes Control of eDiscovery Process with Symantec’s Clearwell eDiscovery Platform">Nikon Corp. Takes Control of eDiscovery Process with Symantec's Clearwell
- 03/20 http://www.symantec.com/about/news/release/article.jsp?prid=20120320_02 Symantec-Sponsored Ponemon Report Finds Negligent Employees Top Cause of Data Breaches in the U.S. While Malicious Attacks Most Costly">Ponemon Report Finds Negligent Employees Top Cause of U.S. Data Breaches
- 03/20 http://www.symantec.com/about/news/release/article.jsp?prid=20120320_01 Symantec to Acquire Nukona to Help Businesses Embrace “Bring Your Own Device” Movement">Symantec to Acquire Nukona
- 03/19 http://www.symantec.com/about/news/release/article.jsp?prid=20120319_01 Symantec Corporation Named One of the World's Most Ethical Companies for 2012">Symantec Named To List Of World's Most Ethical Companies for 2012
- 03/14 http://www.symantec.com/about/news/release/article.jsp?prid=20120314_01 Experian and Symantec's two-factor credentialing solution selected by Centers for Medicare & Medicaid Services">Symantec Selected by CMS for Validation and ID Protection Service
- 03/13 http://www.symantec.com/about/news/release/article.jsp?prid=20120313_01 Symantec Announces Global Availability of NetBackup 7.5 and Backup Exec 2012">Symantec Announces Availability of NetBackup 7.5 and Backup Exec 2012
- 03/12 http://www.symantec.com/about/news/release/article.jsp?prid=20120312_02 Symantec Helps Organizations Get Control of Runaway Data Growth">Symantec Helps Organizations Get Control of Runaway Data Growth
- 03/06 http://www.symantec.com/about/news/release/article.jsp?prid=20120306_02 Norton Mobile Security Protects Samsung GALAXY Smartphone Users Worldwide">Norton Mobile Security Protects Samsung GALAXY Smartphone Users Worldwide
- 03/06 http://www.symantec.com/about/news/release/article.jsp?prid=20120306_01 Autodesk Selects Symantec’s Clearwell eDiscovery Platform">Autodesk Selects Symantec’s Clearwell eDiscovery Platform
- 02/29 http://www.symantec.com/about/news/release/article.jsp?prid=20120229_01 Symantec Report Finds New Wave of Cyber-attacks Impersonating Business Mediation and Arbitration Service and Volume of Spam Increases Around Valentine’s Day">Symantec Report Finds Wave of Cyber-attacks Impersonating Business Service
- 02/28 http://www.symantec.com/about/news/release/article.jsp?prid=20120228_02 Symantec and VMware Partner to Deliver Extensive Protection for Virtual and Cloud Environments">Symantec and VMware Partner to Protect Virtual and Cloud Environments
- 02/28 http://www.symantec.com/about/news/release/article.jsp?prid=20120228_01 Symantec O<sub>3</sub> Delivers New Security Control Point for the Cloud">Symantec O3 Delivers New Security Control Point for the Cloud
- 02/27 http://www.symantec.com/about/news/release/article.jsp?prid=20120227_01 Symantec Advances Enterprise Mobility Strategy, Delivers New Innovations to Improve Data Security and Facilitate Broader Application Adoption">Symantec Advances Enterprise Mobility Strategy, Delivers New Innovations
- 02/21 http://www.symantec.com/about/news/release/article.jsp?prid=20120221_02 Symantec Survey Reveals Significant Adoption of Enterprise Mobile Apps, IT Focuses on Balancing Benefits and Risks">Symantec Survey Reveals Significant Adoption of Enterprise Mobile Apps.
- 02/21 http://www.symantec.com/about/news/release/article.jsp?prid=20120221_01 Symantec and FairWarning Help Assure Compliance with Federal and State Privacy Healthcare Laws">Symantec and FairWarning Help Compliance with Healthcare Privacy Laws
- 02/16 http://www.symantec.com/about/news/release/article.jsp?prid=20120216_02 Symantec Receives Parallels 2011 APS ISV Service of the Year Award">Symantec Receives Parallels 2011 APS ISV Service of the Year Award
- 02/16 http://www.symantec.com/about/news/release/article.jsp?prid=20120216_01 Symantec Positioned as a Leader in the Client Management Tools Magic Quadrant">Symantec Positioned as a Leader in Client Management Tools Magic Quadrant
- 02/15 http://www.symantec.com/about/news/release/article.jsp?prid=20120215_05 Norton 360 Everywhere Extends Powerful Protection to Multiple Devices">Norton 360 Everywhere Extends Powerful Protection to Multiple Devices
- 02/15 http://www.symantec.com/about/news/release/article.jsp?prid=20120215_03 Symantec Leverages New Parallels Automated Platforms to Deliver Cloud Services to SMBs">Symantec Leverages Parallels Platforms to Deliver Cloud Services to SMBs
- 02/15 http://www.symantec.com/about/news/release/article.jsp?prid=20120215_02 Norton One to Deliver Comprehensive Security with Personalized Service">Norton One to Deliver Comprehensive Security with Personalized Service
- 02/15 http://www.symantec.com/about/news/release/article.jsp?prid=20120215_01 Top 10 “Riskiest” Online Cities of 2012 Presented by Norton">Top 10 “Riskiest” Online Cities of 2012 Presented by Norton
- 02/14 http://www.symantec.com/about/news/release/article.jsp?prid=20120214_01 Symantec Provides Business Perspective on IT Risk with New Risk and Compliance Solution">Symantec Provides Business Perspective on IT Risk with New IT GRC Solution
- 02/07 http://www.symantec.com/about/news/release/article.jsp?prid=20120207_02 Norton Online Family Expands to Keep Kids Safe on Mobile Phones">Norton Online Family Expands to Keep Kids Safe on Mobile Phones
- 02/07 http://www.symantec.com/about/news/release/article.jsp?prid=20120207_01 Symantec Unveils New Global Security Operations Center in U.S.">Symantec Unveils New Global Security Operations Center in U.S.
- 02/06 http://www.symantec.com/about/news/release/article.jsp?prid=20120206_02 Symantec NetBackup Ends the Backup Window with 100 Times Faster Backups">Symantec NetBackup Ends the Backup Window with 100x Accelerated Backups
- 02/06 http://www.symantec.com/about/news/release/article.jsp?prid=20120206_01 Symantec Declares Better Backup for All Sized Organizations and Calls for 80 Percent Reduction in Operating Costs">Symantec Declares Better Backup and 80% Reduction in Operating Costs
- 02/03 http://www.symantec.com/about/news/release/article.jsp?prid=20120203_03 Symantec Releases Backup Exec Dedicated to 100 Percent Virtual Environments and Expands Data Protection for Small Businesses">Symantec Releases Backup Exec Dedicated to 100% Virtual Environments
- 01/31 http://www.symantec.com/about/news/release/article.jsp?prid=20120131_01 Norton Identity Safe Beta Now Available for Free Download">Norton Identity Safe Beta Now Available for Free Download
- 01/26 http://www.symantec.com/about/news/release/article.jsp?prid=20120126_03 Stephen Gillett Appointed to Symantec Board of Directors">Stephen Gillett Appointed to Symantec Board of Directors
- 01/26 http://www.symantec.com/about/news/release/article.jsp?prid=20120126_02 Symantec to Speak at Upcoming Investor Conferences">Symantec to Speak at Upcoming Investor Conferences
- 01/26 http://www.symantec.com/about/news/release/article.jsp?prid=20120126_01 Symantec Report Finds Spammers are Taking Advantage of New Year Holidays and Major Events">Symantec Report Finds Spammers are Taking Advantage of New Year Holidays
- 01/25 http://www.symantec.com/about/news/release/article.jsp?prid=20120125_02 Symantec Authorizes $1 Billion Share Repurchase Program">Symantec Authorizes $1 Billion Share Repurchase Program
- 01/25 http://www.symantec.com/about/news/release/article.jsp?prid=20120125_01 Symantec Reports Record Third Quarter Fiscal 2012 Results">Symantec Reports Record Third Quarter Fiscal 2012 Results
- 01/23 http://www.symantec.com/about/news/release/article.jsp?prid=20120123_01 Symantec’s Clearwell eDiscovery Platform To Offer Transparent Predictive Coding To Enable Rapid and Defensible Automated Document Review">Clearwell eDiscovery Platform To Offer Transparent Predictive Coding
- 01/19 http://www.symantec.com/about/news/release/article.jsp?prid=20120119_02 Symantec Positioned in Leading Analyst Firm’s Leaders Quadrant for Endpoint Protection Platforms">Symantec Positioned in Leaders Quadrant for Endpoint Protection Platforms
- 01/19 http://www.symantec.com/about/news/release/article.jsp?prid=20120119_01 Extendicare Health Services Takes eDiscovery In-House with Symantec’s Enterprise Vault and Clearwell eDiscovery Platform">Extendicare Takes eDiscovery In-House with Enterprise Vault and Clearwell
- 01/16 http://www.symantec.com/about/news/release/article.jsp?prid=20120116_01 Symantec Announces Intelligent Information Governance to Mitigate Risks and Free Information">Symantec Announces Intelligent Information Governance Solution
- 01/09 http://www.symantec.com/about/news/release/article.jsp?prid=20120109_01 Symantec Shows Largest Growth in SSL Certificates, Dominating the EV SSL Market">Symantec Shows Largest Growth in SSL Certificates and EV SSL Market
- 01/03 http://www.symantec.com/about/news/release/article.jsp?prid=20120103_01 Symantec to Webcast Quarterly Earnings Call">Symantec to Webcast Quarterly Earnings Call
Risk Maturity – What's Your Score?
When it comes to risk maturity, how do you rank? Identifying, assessing and prioritizing your risks are more important than ever to defend against threats, enable compliance, and capitalize on new business and revenue opportunities. Take a broader view of risk management by looking at just how risky your organization is. http://go.trustwave.com/815RFM693000026003o4f00
BYOD Beware
Businesses are embracing BYOD, and mobile applications are becoming the preferred platform for users and customers to access data and conduct transactions. In fact, 75% of businesses let employees use their own devices to access their network.* What risks lurk behind this mobile revolution? *Trustwave Infographic: The High Cost of BYOD http://go.trustwave.com/815RFM693000027003o4f00
Get in Touch With Your Dark Side
Hackers are making headlines every day, and if you’re not prepared, you may be opening the door to unnecessary risk. Teaching your employees to “think like the bad guys” can help close the door on your next attack. http://go.trustwave.com/815RFM693000028003o4f00
Trustwave Announces SSL SHA-2 Support
As you may know there have been a few announcements regarding the browser and Certification Authority industries replacing the SHA-1 hashing algorithm with the more secure SHA-2. Microsoft, Google and Mozilla have all announced various plans to stop supporting SHA-1 SSL certificates after January 1, 2017.
Trustwave will offer full support for SHA-2 (aka SHA-256) certificates effective October 29, 2014. On this date the following options will be available through the Trustwave SSL Control Center and Partner APIs:
- Ability to issue SSL certificates using the SHA-2 hashing algorithm
- All new certificates will default to SHA-2
- SHA-1 is still an option with a limited expiration date
- All existing SHA-1 certificates can be re-issued as SHA-2 free of charge.
On January 1, 2015 the following policies will go in to effect:
- No new SHA-1 code signing certificates will be issued
- All new SHA-1 certificates (DV, OV and EV) will only be valid for 1 year.
On January 1, 2016 the following policy will go in to effect:
- No new SHA-1 certificates of any kind will be issued.
Trustwave encourages all customers to begin testing SHA-2 certificates as soon as possible. This is especially important with the accelerated schedule from Google. Our SSL certificate analyzer page will help you evaluate your existing certificates against the Google deadlines to see what user interface changes Chrome users will see.
Many browser, operating system and application vendors are releasing patches and new versions that support SHA-2. Trustwave has a SHA-2 compatibility page found here. SHA-2 support comes from these vendors, not the SSL certificate, so you will need to work with your vendors to determine the most up-to-date SHA-2 compatibility.
Trustwave fully supports the move to SHA-2 and is here to help you any way we can. We have created a special SHA-2 support page to help you get started. This SHA-2 support page contains information on browser and operating system compatibility, a link to our SSL test page as well as our SHA-2 FAQ. If you have any questions about SHA-2 please don’t hesitate to contact Trustwave SSL Support by calling 1-866-SSL-CERT (775-2378) or email at sslsupport@trustwave.com.
The 2013 Trustwave Global Security Report gives you needed perspective by analyzing the latest threats and vulnerabilities facing organizations just like yours. We’ve gathered insight from:
• hundreds of incident response investigations
• thousands of penetration tests
• millions of website and Web application attacks
• and tens of billions of events- 06/12/2012https://www.trustwave.com/pressReleases.php?n=trustwave-takes-on-targeted-attacks-new-security-solutions" target=_blank>Trustwave Takes On Targeted Attacks with New Security Solutions
- 05/25/2012https://www.trustwave.com/pressReleases.php?n=trustwave-wins-two-security-industry-awards-sc-congress-canada" target=_blank>Trustwave Wins Two Security Industry Awards at SC Congress Canada
- 05/04/2012https://www.trustwave.com/pressReleases.php?n=trustwave-wins-prestigious-awards-innovation-best-anti-malware" target=_blank>Trustwave Wins Prestigious Awards for Innovation and Best Anti-Malware Solution
- 03/29/2012https://www.trustwave.com/pressReleases.php?n=trustwave-named-a-leader-managed-security-services-by-independent" target=_blank>Trustwave Named a Leader in Managed Security Services by Independent Research Firm
- 03/19/2012https://www.trustwave.com/pressReleases.php?n=vigil-software-appointed-as-a-uk-distributor-trustwave-" target=_blank>Vigil Software appointed as a UK distributor for Trustwave
- 03/19/2012https://www.trustwave.com/pressReleases.php?n=trustwave-completes-acquisition-m86-security" target=_blank>Trustwave Completes Acquisition of M86 Security
- 03/06/2012https://www.trustwave.com/pressReleases.php?n=trustwave-to-acquire-m86-security" target=_blank>Trustwave to Acquire M86 Security
- 02/23/2012https://www.trustwave.com/pressReleases.php?n=trustwave-unveils-new-managed-security-services" target=_blank>Trustwave Unveils New Managed Security Services
- 02/22/2012https://www.trustwave.com/pressReleases.php?n=trustwave-named-finalist-seven-sc-magazine-awards-europe-us" target=_blank>Trustwave Named Finalist for Seven SC Magazine Awards in Europe and U.S.
- 02/13/2012https://www.trustwave.com/pressReleases.php?n=trustwave-announces-healthcare-partnership-with-jgo-labs" target=_blank>Trustwave Announces Healthcare Partnership with JGo Labs
- 02/07/2012https://www.trustwave.com/pressReleases.php?n=trustwave-report-reveals-global-data-breach-and-security-trends" target=_blank>Trustwave Report Reveals Global Data Breach and Security Trends
- 02/02/2012https://www.trustwave.com/pressReleases.php?n=trustwave-simplifies-pci-compliance-for-small-merchants%20" target=_blank>Trustwave Simplifies PCI Compliance for Small Merchants
Thawte has adopted the latest Certificate Authority Browser Forum standards designed to further strengthen the s ecurity and trust that comes with SSL Certificates. Based on these new guidelines, Thawte SSL has incorporated the following changes:
- The maximum SSL certificate validity period is now 4 years. SSL certificates issued after April 1, 2015 will have a maximum validity period of 3 years. Extended Validation (EV) certificates will continue to remain valid for 2 years.
- The Common Name (CN) will be added to the Subject Alternative Name (SAN) field at no additional charge.
- After October 2015, Thawte will not issue a certificate containing a Reserved IP address or Internal Server Name that has an expiration date later than November 1, 2015.
- Thawte will include an Object Identifier (OID) to uniquely identify a Thawte SSL certificate and will use locality, state, and country data based on pre-vetted information, not information from the certificate signing request. These changes will be effective on or before July 1, 2012.
8/09/2014
We’d like to make you aware of upcoming changes that will affect how websites that use SHA-1 certificates are displayed in Google browsers.
As previously communicated, SHA-1 will be completely phased out in the next couple of years. In order to encourage prompt adoption of more secure algorithms, Google is making changes to its user interface from Google Chrome 39 to degrade websites that use SHA-1 certificates. The changes will start in November 2014.
- Check which algorithm an SSL Certificate uses via our SSL checker.
- If the website uses a SHA-1 SSL Certificate that expires later than 12/31/2015, the certificate will need to be reissued to SHA-256. Reissues are free.
- If their applications do not support SHA-256, we strongly recommend they upgrade them as soon as possible.
22/07/2014
39 Month Maximum Certificate Validity: April 2015
Requirement: Beginning April 01, 2015, certificates will be limited to a maximum validity of 39 months.
Important Upcoming Dates
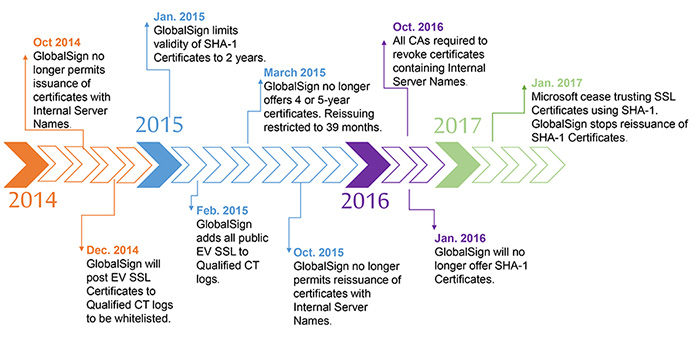
- March 29, 2015: GlobalSign will no longer offer 4 or 5-year certificates. Reissuing of certificates will be limited to a maximum of 39 months. This also applies to certificates issued when adding or removing SANs.
Please note:
All customers who purchase 4 or 5 year certificates today will be impacted when they attempt to reissue their certificate. If a customer reissues a certificate after April 2015 that contains a validity period longer than 39 months, the validity period will be truncated because certificates can only be reissued for the first 39 months of life. GlobalSign's ordering system currently warns users of these upcoming changes if they choose to purchase a 4 or 5 year certificate.
39 Month Maximum Re-use of Vetting Information: April 2015
Requirement: Beginning April 01, 2015 certificate data used to verify the certificate information is only valid for up to 39 months (this applies to issuance and reissuance). When issuing a certificate, the data used for issuance (enterprise vetting and domain control) must be less than 39 months old. If the data is older than 39 months, then the data must be revalidated prior to issuing a new certificate.
Important Upcoming Dates:
- March 29, 2015: GlobalSign limits reissuance to the first 39 months of certificate validity.
Please note:
All customers who purchase 4 or 5 year certificates today will be impacted when they attempt to reissue their certificate. If a customer reissues a certificate after April 2015 that contains a validity period longer than 39 months, the validity period will be truncated because certificates can only be reissued for the first 39 months of life. GlobalSign's ordering system currently warns users of these upcoming changes if they choose to purchase a 4 or 5 year certificate.
Internal Server Name Deprecation: Nov 2015
Requirement: On November 22nd, 2011, the CA/Browsers Forum outlined the following Baseline Requirement: "The CA shall not issue a certificate with an expiration date later than November 1st, 2015 with a SAN or Subject Common Name field containing a Reserved IP address or Internal Server Name. Effective October 1st, 2016, CAs are required to revoke all unexpired certificates whose SAN or Subject Common Name field contains a Reserved IP Address or Internal Sever Name.
Important Upcoming Dates:
- October 26, 2014: GlobalSign will not permit the issuance of certificates with Internal Server Names
- October 31, 2015: GlobalSign will not reissue any certificates with Internal Server Names.
Deprecation of SHA-1: January 2017
Requirement: Beginning January 1st 2017 Microsoft will stop trusting SHA-1 Certificates issued under public roots. This applies to all SSL, Code Signing, Client Certificates and CA Certificates (except Root CA certificates) issued under publically trusted roots. While the CA/B Forum is yet to specify that SHA-256 encryption must be used in their Baseline Requirements, GlobalSign has decided to support the industry decision lead by Microsoft.
Important Upcoming Dates:
- January 2015: The maximum validity of GlobalSign SHA-1 SSL certificates will be changed from 3 years to 2 years.
- January 2016*: GlobalSign will no longer offer Certificates with the SHA-1 hashing algorithm
- January 2017*: GlobalSign will no longer re-issue SHA-1 Certificates.
- January 2017*: Microsoft will cease trusting SSL certificates using SHA-1
- *If Microsoft should change its date of January 2017, GlobalSign may review its associated dates.
Please Note:
Users are urged to obtain SHA-256 Certificates and verify there are no issues with their web clients or legacy systems. In the event a SHA-256 Certificate does not support your needs, you may reissue to a SHA-1 Certificate.
Certificate Transparency ( RFC 6962 )
Requirement: Beginning February 1st 2015, Google Chrome will not display the Green Bar associated with EV SSL Certificates if the certificate is not Certificate Transparency (CT) compliant.
Certificate Transparency (CT) is being promoted by Google to help enterprise users detect possible mis-issuance of certificates. The requirement involves posting EV SSL Certificates to publically accessible Qualified CT Logs. These logs can be monitored by enterprises and they can track issuance of certificates to their domains and then take corrective action if mis-issuance has been detected. If EV SSL Certificates are not CT compliant, then Chrome will not display the distinctive green bar starting in February 2015.
GlobalSign will be posting all publically visible EV SSL Certificates to qualified CT logs in 2014 in order to have them added to the Google CT whitelist. Those certificates not visible on the internet will not be posted unless requested by a customer. In the event that an EV Certificates is not whitelisted, it can be reissued and posted at that time. Starting in January 2015, EV certificates will be published to the CT logs during issuance by default; however, users will be able to opt out of this if they do not want CT compliant certificates (certificates used internally which may disclose internally accessible server names which they consider sensitive). GlobalSign ordering pages and APIs will be updated to allow users to opt-out of CT when ordering EV Certificates.
Important Upcoming Dates:
- December 2014: GlobalSign will post all publically accessible EV SSL Certificates to one or more Qualified CT logs to be whitelisted.
- December 2014: GlobalSign will update the ordering pages and APIs to allow users to opt-out of CT. The default will be to issue EV SSL Certificates that are CT compliant.
12/03/2014
Following on from our announcement in February, we would like to remind you that GlobalSign will be making SHA-256 Certificates available to support the industry-wide movement away from the SHA-1 hashing algorithm.┬а With nearly 3 years until the Microsoft announced January 2017 deadline for SHA-1 deprecation of SSL Certificates, we are providing you the ability to obtain both SHA-1 and SHA-256 SSL Certificates to facilitate your transition.┬а
SSL Customers
Commencing March 31st 2014, all GlobalSign SSL Certificates will default to using the stronger SHA-256 algorithm; with SHA-1 available during the ordering process as an option should your legacy applications still require it. All existing SSL Certificates can also be reissued and upgraded from SHA-1 to SHA-256 and vice versa at any time with no additional charge. Please note that due to the Microsoft imposed 2017 deadline for not trusting SHA-1 Certificates, 4 and 5 year SHA-1 Certificates will no longer be available.SSL Customers already receiving SHA-256 Certificates
If you are already receiving SHA-256 SSL Certificates today, your account will automatically be updated to align with the new SHA-256 offering. This means that you will receive SHA-256 Certificates under the GlobalSign Root 1 (vs. Root 3) and a different intermediate CA.Code Signing, PersonalSign and existing EPKI Customers
Also from March 31st 2014, all new GlobalSign Code Signing and PersonalSign Certificates will default to using the stronger SHA-256 algorithm; with SHA-1 available as an option. Legacy EPKI accounts will continue to offer SHA-1 as a default setting and SHA-256 as an option. Further details regarding the migration to the GlobalSign SHA-256 based certificate hierarchy will be forthcoming
С 1 июня GlobalSign прекращает выпуск Code Signing сертификатов для физических лиц
Please be aware that from 1st June 2013 GlobalSign will no longer be offering Code Signing Certificates for Individuals. This change of offering is due to GlobalSign’s aim to ensure the highest level of security best practices.
Once the Individual Level Certificate expires you will need to upgrade to the Software Vendor/Organisation level Code Signing Certificate to continue your service with GlobalSign. To obtain a Software Vendor & Organisation level Code Signing Certificate you will need to be a legally registered business entity.
We are delighted to share the latest improvements we have made to the load time of secure web pages using GlobalSign SSL Certificates.
GlobalSign has partnered with CloudFlare to benefit from their 23 data centres around the world to deliver certificate statuses, accelerating the loading speed of SSL pages and optimising the browsing experience of millions of end users.
For the first time in our industry, GlobalSign has combined SSL security and web performance as the new partnership allows our customers to:
- Eliminate website response delays associated with traditional SSL
- Reduce visitors’ waiting times and increase loyalty and conversions
- Operate with peak efficiency, fast performance and strong security
GlobalSign is the first CA to take on this innovative approach, delivering the fastest SSL page load speed available today. As web developers and online marketeers invest heavily into website performance, choosing the right Certification Authority does matter.
Server Gated Cryptography (SGC) and its Limited Value
SGC was originally designed to force weak 40 encryption browsers versions to use stronger 128 bit encryption, based on the US cryptography export restrictions of the mid-1990s. The use of SGC will upgrade weak encryption, but this does not address the many security vulnerabilities that are present in these browsers. Such exploits leave the SGC browsers vulnerable to attack via man in the middle attacks, botnet infection, keylogging and malware infection.
GlobalSign firmly believes that SGC Band-Aids over more serious vulnerabilities. The object of SGC is defeated if a potential attacker can exploit a security weakness in the browser or the protocol that is not related to encryption strength. Users who want stronger security should therefore keep their software up to date. As a result GlobalSign now only provides SGC as an option and does not integrate this by default with its SSL Certificates. We do not believe that SGC provides any real value in today’s Internet ecosystem, and discourage partners from promoting its use.
GlobalSign would like to make you aware of a number of important changes that will be taking place to meet the upcoming CABForum Baseline Requirements for the issuance and management of SSL Certificates.
1. SSL Issuance to Hostnames, Internal IPs and Non-FQDNs
GlobalSign will no longer accept requests to include shortnames within the Subject Alternative Name extension of Domain Validated SSL Certificates with validity periods exceeding 15th November 2015.This change is due to new policy requirements enforced by the CABForum. See Section 9.2.1 - page 9 http://www.cabforum.org/Baseline_Requirements_V1.pdf
This will affect GlobalSign customers who are currently using the Subject Alternative Name field for the issuance of hostnames and non-FQDNs within Domain Validated SSL Certificates.
Please note that if you have already been issued a certificate with a SAN containing a shortname, you do not need to take any action and this will continue working as normal.
2. Unverified Information in SSL Organization Unit Field
GlobalSign will no longer accept un-verifiable information in the certificate’s subject:organizationlUnitName (OU) field.New policy requirements enforced by the CABForum stipulate that no misleading information may be contained in the certificate. See Section 9.2.6 - page 10 http://www.cabforum.org/Baseline_Requirements_V1.pdf
GlobalSign will update vetting practices to include validation of the OU field.
Moving forward, the OU field will be hard coded into certificate profiles. Customers wishing to create different OU fields will be able to use the multiple profile feature within a Managed SSL Account.
3. Certificate Validity Periods
GlobalSign will only allow certificate issuance with validity periods up to a maximum of 60 months.This change is due to the CABForum Baseline Requirements. See Section 9.4 - page11
http://www.cabforum.org/Baseline_Requirements_V1.pdfThis does not affect existing GlobalSign SSL Certificate customers.
4. Verification of Country for Domain Validated SSL Certificates
GlobalSign will no longer place unverifiable country codes in the subject:countryName field for Domain Validated SSL Certificates (including DomainSSL and AlphaSSL Certificates).
New policy requirements enforced by the CABForum include an update regarding the accuracy of information for certificate fields. See Section 9.2.5 - page 10 http://www.cabforum.org/Baseline_Requirements_V1.pdf
This does not affect existing GlobalSign SSL Certificate customers.
Security Incident Report
We didn't find any evidence of
- Rogue Certificates issued.
- Customer data exposed.
- Compromised GlobalSign Root Certificate keys and associated Hardware Security Modules (HSM).
- Compromised GlobalSign Certificate Authority (CA) infrastructure.
- Compromised GlobalSign Issuing Authorities and associated HSMs.
- Compromised GlobalSign Registration Authority (RA) services.
What did happen
- Peripheral web server, not part of the Certificate issuance infrastructure, hosting a public facing web property was breached.
- What could have been exposed? Publicly available HTML pages, publicly available PDFs, the SSL Certificate and key issued to http://www.globalsign.com .
- SSL Certificate and key for http://www.globalsign.com were deemed compromised and revoked.
- New Certificate issuance temporarily halted between 6th and 15th September.
- During outage:
- GlobalSign contracted Fox-IT to provide third party analysis of the GlobalSign infrastructure. Fox-IT were also retained by the Dutch Government as part of the ongoing Comodohacker criminal investigation.
- GlobalSign contracted Cyber Security Japan to oversee the rebuild of a newly hardened Certificate issuance infrastructure, on the now disproven assumption that previous infrastructure had been breached. - The self-titled attacker "Comodohacker" has been assumed to be a credible threat to security providers, in particular Certificate Authorities, since the attack made by the Comodohacker on a Comodo RA Partner resulted in the issuance of rogue Certificates by Comodo in March 2011.
- A post was made on 5th September by the Comodohacker via the Pastebin service claiming responsibility for the DigiNotar hack.
- The same post also stated that several other CAs had been compromised, including a reference to GlobalSign.
- GlobalSign deemed the threat credible and immediately began a thorough network analysis, assuming a highly sophisticated attack had been executed on, or was in process against, multiple Certificate Authorities.
- On 6th September, even though the non-specific Comodohacker claims were yet to be substantiated, GlobalSign deemed the most responsible reaction was to halt issuance of new Certificates in order to:
- Accelerate the investigation.
- Protect against issuance of rogue Certificates should the claims be true. - On 9th September, the investigative team found evidence of a breach to the web server hosting the http://www.globalsign.com website. The breached web server (located in a hosting facility in North America) was a peripheral web server located externally (both logically and geographically seperate) from the GlobalSign Certificate issuance infrastructure. GlobalSign immediately assumed the contents of the web server were compromised, including:
- All public facing HTML files.
- All public facing documents and PDF files.
- The http://www.globalsign.com SSL Certificate and key. - The www.globalsign.com domain is used only for the externally facing North American web sites and runs no web applications capable of requesting or issuing Certificates nor does it hold any customer data.
- The SSL Certificate for http://www.globalsign.com was revoked.
- The breached web server was immediately locked down and subsequently rebuilt with a new disk and hardened system image.
- In parallel additional security precautions were taken, including:
- GlobalSign Certificate infrastructure was rebuilt with new hardware and hardened images for all services.
- Additional IDS (Intrusion Detection Services) were deployed to certificate related services.
- Enhanced internal controls have been placed around logical access to issuance systems.
- Operational environment for Internet facing systems has been hardened further. - On September 15th services were brought back online. All customer account passwords were reset as part of bringing the service back online.
- GlobalSign maintains an offline root, and has done since 1996.
- An offline root means that the GlobalSign Root Certificate key material is not connected to any network of any type. Root key material is physically (geographically) separate from any networked systems and is only ever exercised in controlled, and physically sealed offline ceremonies. - GlobalSign has never directly issued end entity Certificates using the Root Certificate, instead only ever issuing off Subordinate Certificates (also referred to as the Issuing Authority). In the event of a compromise this would not require the revocation of the entire PKI but only the compromised Subordinate Certificate.
- Fox-IT has been contracted to provide ongoing security consultancy.
- All issuance and Internet facing infrastructure is now monitored 24/7 through a managed IDS service.
- Transparent incident response and issuance practices.
- Continuous auditing of network and security infrastructure.
- Standards for operational and vetting practices.
- Technology and processes for speedy response to such security incidents.
- Formal collaboration between global authorities and security providers.
- Many international authorities maintain detailed profiles of the Comodohacker and other actors, and continue to build a more accurate picture with evidence gathered and volunteered by many industry members.
- GlobalSign, like other security providers, continues to share threat information and collaborate closely with all appropriate authorities.
- Compliance - Browsers are in compliance with certificate rules (1024 to 2048 migration); in alignment with CAB/F requirements rendering tighter security protecting your clients' online security reputation.
- Performance - Improved speed and robust automation, allowing cradle to grave purchasing, and authentication to be more efficient resulting in client satisfaction.
- Time to Market - Platform consolidation will provide partners with access to new products and features in a more timely manner, thereby driving increased revenue and partner profitability.
- GeoTrust True Business ID
- GeoTrust True Business ID Wildcard
- GeoTrust True Business ID with EV
- GeoTrust Quick SSL
- GeoTrust Quick SSL Premium
- RapidSSL
- RapidSSL Wildcard
- 10/20/2011 http://www.geotrust.com/about/news/GeoTrust-launches-web-site-anti-malware-scan/index.html GeoTrust Launches Web Site Anti-Malware Scan Exclusively Through Channel
- 08/08/2011 http://www.geotrust.com/about/news/GeoTrust-SSL-certificates-help-vacationers-keep-cool/index.html GeoTrust SSL Certificates Help Summer Vacationers Keep Their Cool When Booking Travel Online
- 02/04/2011 http://www.geotrust.com/about/news/GeoTrust-shows-consumers-are-covered-for-kick-off/index.html GeoTrust Shows Consumers Are Covered for Kick-Off
- 01/27/2011 http://www.geotrust.com/about/news/GeoTrust-ranked-number-one-SSL-certificate-provider/index.html GeoTrust Ranked No. 1 SSL Certificate Provider among Top 1 Million Websites
- 01/04/2011 http://www.geotrust.com/about/news/GeoTrust-leads-SSL-index-for-seventh-consecutive-month/index.html GeoTrust Leads Index of Most Visited Websites for Seventh Consecutive Month
- 11/30/2010 http://www.geotrust.com/about/news/Top-Websites-Choose-GeoTrust-SSL-Certificates-for-Site-Encryption/index.html Majority of World's Top Websites Choose GeoTrust SSL Certificates for Cost Effective Site Encryption
- 11/05/2010 http://www.geotrust.com/about/news/GeoTrust-Takes-Aim-at-Extending-Its-Lead-in-Low-Cost-SSL-Market/index.html GeoTrust Takes Aim at Extending Its Lead in Low-Cost SSL Market
- 10/11/2010 http://www.geotrust.com/about/news/GeoTrust-beats-GoDaddy-for-SSL-market-share/index.html GeoTrust Again Beats Go Daddy in Race for SSL Market Share Among Top Websites
- 08/31/2010 http://www.geotrust.com/about/news/GeoTrust-is-ssl-provider-of-choice/index.html ‘Alexa Netcraft Index’ Once Again Shows GeoTrust Is the SSL Provider of Choice Among Web Sites that See the Highest Traffic
- 08/04/2010 http://www.geotrust.com/about/news/most-visited-web-sites-rely-on-GeoTrust/index.html Internet's Most-Visited Web Sites Rely on GeoTrust SSL More than Any Other Certificate Authority
- 07/06/2010 http://www.geotrust.com/about/news/most-visited-domains-rely-on-GeoTrust/ Internet's 1 Million Most-Visited Domains Rely on GeoTrust SSL More Than Any Other Certificate Authority
- 20 June 2012 http://www.comodo.com/news/ SSL Providers and Nginx, Inc. improve Online Trust through Enhanced Certificate Revocation Checking, sign a Sponsorship Agreement
- 15 May 2012 Comodo and TeleSign Partner to Deliver Intelligent Authentication
- 04 Apr 2012 Comodo's New CCloud Windows and Android Clients Make It Easier To Synchronize, Upload, Download and Share Files
- 20 Mar 2012 Comodo Breaks Ground with Mobile App Enabling Small Business IT Staff to Manage Endpoint Security from Smartphones
- 28 Feb 2012 Matousec's Proactive Security Challenge hails a Comodo Internet Security Product as No. 1.
- 20 June 2012 more Major SSL Providers and Nginx, Inc. improve Online Trust through Enhanced Certificate Revocation Checking, sign a Sponsorship Agreement
- 15 May 2012 Comodo and TeleSign Partner to Deliver Intelligent Authentication
- 04 Apr 2012 Comodo launches SiteInspector - free malware scanning and blacklist monitoring for websites
- 27 Mar 2012 Comodo's New CCloud Windows and Android Clients Make It Easier To Synchronize, Upload, Download and Share Files
- 20 Mar 2012 Comodo Launches Consumer Advocacy Campaign
Impact to Customers
GlobalSign adopted a high threat response to the claims that unfortunately resulted in 9 days of service disruption, specifically:
Timeline
This timeline covers events from 5th September to 15th September 2011.
Controls - mitigating against future attacks
GlobalSign, with the help of Fox-IT, found no evidence that the GlobalSign Certificate issuance infrastructure was compromised. However, GlobalSign has implemented additional controls around infrastructure, customer data protection and access to all systems. It is our view that this attack is one phase of an advanced persistent threat against all security solution providers. Because the threat landscape has evolved, GlobalSign believes greater controls are necessary across the industry and echoes the calls covered in WebTrust 2.0 and the recent updates to the Mozilla Root CA acceptance program. In response to such requirements, GlobalSign specifically confirms:
Additionally, GlobalSign wishes to restate to customers and partners that physically geographic and logical separation is maintained between critical infrastructure applications, including web servers, order processing applications, CRM, RA applications, Certificate issuance applications and Root Certificates.
GlobalSign Executive Team Response
As one of the longest operating Certification Authorities, the worldwide GlobalSign team is aware of the impact to customers and partners of halting Certificate issuance for any period of time. The executive team apologizes sincerely for the inconvenience caused when undertaking such an important decision. However the organization stands by the decision and maintain that the ultimate duty of care for GlobalSign, like all responsible CAs, is to avoid issuance of rogue Certificates.
We are truly thankful for the positive reaction to our chosen response to the incident, including the press covering this and other incidents, our peers, and ultimately from our valued customers and partners.
GlobalSign has learned much from this incident. More than ever, we appreciate that the threat has evolved, and we are committed to ensuring no such outages occur again from future claims or attacks. In the period since the claims, we have invested significantly in additional security measures and monitoring and suggest other CAs and security providers align to self-regulate to ensure that:
1. Infrastructure is designed and managed in such a way that it is resilient to attack.
2. In the event of a successful attack, swift and appropriate measures are put into place to mitigate the impact.
3. Incident responses are open and transparent allowing Relying Parties the visibility into the risks they may be exposed to.
As an active participant in the CA/B Forum, GlobalSign is a strong supporter of the industry's continued definition and adoption of:
Such efforts include the CA/B Forum's minimum guidelines, Mozilla's CA security controls and any future industry initiatives that serve in the best interest of PKI and Internet security in general.
Finally, we also support ongoing co-operation between the security providers, CAs and the various global authorities in sharing threat information promptly and accurately.
Ongoing Authority Involvement
Definitions
As defined in the CA/B Forum Baseline Guidelines - http://www.cabforum.org
Issuing CA: In relation to a particular Certificate, the CA that issued the Certificate. This could be either a Root CA or a Subordinate CA.
Registration Authority (RA): Any Legal Entity that is responsible for identification and authentication of subjects of Certificates, but is not a CA, and hence does not sign or issue Certificates. An RA may assist in the certificate application process or revocation process or both. When "RA" is used as an adjective to describe a role or function, it does not necessarily imply a separate body, but can be part of the CA.
Relying Party: Any natural person or Legal Entity that relies on a Valid Certificate. An Application Software Supplier is not considered a Relying Party when software distributed by such Supplier merely displays information relating to a Certificate.
Root CA: The top level Certification Authority whose Root Certificate is distributed by Application Software Suppliers and that issues Subordinate CA Certificates.
Root Certificate: The self-signed Certificate issued by the Root CA to identify itself and to facilitate verification of Certificates issued to its Subordinate CAs.
Subordinate CA: A Certification Authority whose Certificate is signed by the Root CA, or another Subordinate CA.
GeoTrust NEWS
Changes to GeoTrust and RapidSSL Intermediate CA Root Hierarchy
As part of our ongoing commitment to delivering best-in-class features, security, and economy, we will be upgrading our GeoTrust and RapidSSL Intermediate Root Certificates. Partners and customers will benefit from the intermediate root migration/platform consolidation in the following ways:
This change applies to the following 2048* bit based products and will be managed in two phases to minimize any potential impact to our partners and their customers.
December 5, 2013::
2014:
*All 1024 bit certificates are being discontinued by Dec 31, 2013
Following the upgrade, any new, renewal, and reissue certificate request issued after launch timeframe will require installation of the new intermediate certificate, in addition to the SSL certificate. Any active certificate issued prior to that date will continue to function as normal without further action required.
GeoTrust SSL OCSP Infrastructure Upgrade
The Symantec Website Security Solutions Team will be upgrading our GeoTrust SSL OCSP infrastructure on July 10, 2013
to provide a better experience for our partners and end customers.
The benefit of this change is 15 additional new sites – more sites handling OCSP requests means improved availability and reliability all over the globe.
What this means for your customers:
If your customers’ corporate firewall is configured to allow only a certain set of IP addresses to be accessed from their network, the following actions are required:
1. Add the new IP addresses to your existing list – do not replace or delete the old IP addresses and existing rules for GeoTrust OCSP IP addresses.
2. Discontinuation of support for the nonce extension – clients should not expect a nonce in the response to a request that contains a nonce.
Our OCSP infrastructure upgrade is scheduled for July 10, 2013. Please make sure the new IP addresses are enabled in your customers’ corporate firewall before the upgrade date.
We will be sending out reminders between now and the go-live date. Reminders will also be posted on GeoTrust Partner Center landing page for further enablement. If you experience any issues during the upgrade or have any questions regarding this notice, please contact the GeoTrust Technical Support Team at:
With over 500,000 active certificates installed worldwide, GeoTrust is the largest low-cost SSL certificate provider solely focused on security. Over 300,000 organizations of all sizes in over 170 countries rely on GeoTrust for their digital certificates.
DigiCert’s new EV Code Signing can help your application immediately establish reputation in Microsoft’s SmartScreen® Application Reputation services for Windows® 8 even before the new Operating System launches on October 26. Reputation can allow your users to experience fewer warning messages and have greater confidence and trust in downloading your software.
SmartScreen helps protect users from newly released malware programs, in part by triggering Application Reputation warnings for software files and publishers without sufficiently established reputation. DigiCert’s partnering with Microsoft® last month to integrate our EV Code Signing Certificates with SmartScreen means that your application can immediately establish reputation even if no prior reputation exists for your file or for you as a publisher.
An EV digital signature from DigiCert also helps protect your software from malware, tampering, and theft, and combines the rigorous Extended Validation process with a hardware requirement to safeguard your business identity. Our stringent verification can often be completed in hours instead of the days or weeks required by many of our competitors.
New certificate expands DigiCert's best-in-class offerings
Compatible with Microsoft, new certificates broaden company’s recognized “best in class” SSL certificates to kernel-mode software programmers and engineers.
Lindon, Utah - February 28, 2012 - DigiCert, Inc., an online security provider for many of the most recognized brands and websites in the world, announced that its code signing high-assurance digital certificates are now compatible with Microsoft kernel-mode software. With this extension to its growing product suite, DigiCert becomes one of just a handful of global Certificate Authorities (CA) to offer this service. Microsoft requires developers to digitally sign kernel-mode software for its Windows Vista, Windows 7 and Windows 8 operating systems prior to installation.
“DigiCert continues to broaden its product offerings in response to consumer demand for code signing certificates that are compatible with various operating systems,” said DigiCert Chief Operations Officer Nicholas Hales. “We recognize that today’s network engineers and software developers face increasing responsibilities and security concerns; as with all of our products and services, DigiCert’s kernel-mode certificates are available at competitive rates backed by value-added features and unmatched customer support to increase the efficiency and productivity of the IT department.”
Kernel-mode certificates allow users to digitally sign software and device drivers, which in turn proves identity to users and protects software from being modified after creation. Failing to digitally sign kernel-mode software with a certificate from a reliable third-party leads to a warning in Windows that prevents users from installing any code. DigiCert kernel-mode code signing certificates support Silverlight 4 and work with ActiveX controls, plug-ins and other executables, and they include an optional timestamp to show when the code was signed.
The world’s third-largest issuer of high-assurance digital certificates, DigiCert continues to expand market share through a company focus on enhanced customer value—recently recognized with Frost & Sullivan’s “Best in Class” award—and unmatched support. With the company’s kernel-mode signing, customers get the same quick installation and customer support they have come to expect from a knowledgeable team that is available 24/7 via phone or chat.
WebNotarius® - electronic signature without limits!
Today, we're excited to provide you with the new version of WebNotarius®. The service is the very first widely available, now free of charge validation
service enabling verification of certificates, electronic documents and the validity of electronic signatures used in the European countries, including
all of the European Union. Undoubtedly, this fact will contribute to the elimination of borders and barriers related to electronic signatures use in the
area from Lisbon to Vladivostok. The service is provided by Unizeto Technologies SA, a qualified provider of certification services associated with
the electronic signature - by CERTUM General Certification Authority.
Unizeto, using its experience resulting from the long-standing business in the market of global certification services and due to the cooperation with
many certification authorities as well as using European TSL lists, provides the latest version of the system, which offers a wide range of services,
including the ability to check the status and validity of any kind of over 400 different types of certificates being issued in the EU member states.
It is a real breakthrough in the use of electronic signatures at least on the Community and the Russian market. – said Andrzej Bendig-Wielowiejski,
CEO of Unizeto Technologies SA - Until now in order to verify e-signatures it was required to use various software recommended by each of the nearly
hundreds of working CAs only in the European Union and tens in the Russian Federation. In addition, these applications have been and are only available
for selected operating systems. Now, using any web browser, everyone can visit web pages www.webnotarius.eu or www.webnotarius.pl to easily check
the status and validity of electronic signature or certificate, regardless of the country of origin. This allows the representatives of public administration and
business to secure acceptance of electronic signatures, for instance from Germany, France, Italy, Russia or another country. This is an important step
towards ensuring full interoperability of electronic signatures across Europe.
The service is also available free of charge via the popular SOAP protocol. This enables easy integration with any IT system, therefore allowing for
the full automation of the verification process of certificates and electronic signatures. This is particularly important for software developers, as this will
significantly reduce costs and implementation time of support for the signed electronic document in IT systems.
Qualified certificates provided by Unizeto trusted on a global scale
A report confirming the compliance of qualified certification services provided by Unizeto Technologies SA with the worldwide WebTrust standards set by the
organization AICPA/CICA, was published on August 27, 2010 at https://cert.webtrust.org/ViewSeal?id=1073. Therefore our CERTUM General Certification Authority –
as the only Polish certification authority - is one of the few entities in the world which provide qualified services related to e-signature and are globally trusted.
